Data protection and security
Ideally, all data should be secure, i.e. treated in such a way as to ensure its integrity, authenticity and availability. To reduce the risk of destruction, deterioration, disclosure, falsification, loss, hacking, or theft of data, various actions can be taken :
- Identification of the degree of sensitivity of the data (from "not at all" to "highly")
- Development of a data security policy
- Securing premises and hardware (computers, storage devices, servers, etc.) via single sign-on (SSO) authentication, keys, access codes and passwords
- Backups of all data, at regular intervals and on at least three different media
- Regular updating of environments, software and computer programs
- File authenticity and integrity checks
- Encryption and data encryption
- Checksums for the transmission of messages
- Anonymisation or de-identification of confidential or sensitive data
- Destruction of data
Data security is a different concept from data protection. Protection aims, through laws on the protection of personal data in particular, to protect the personality. It is not the data that is protected or targeted, but the potential harm to the individual that could be caused by the exploitation of the data.
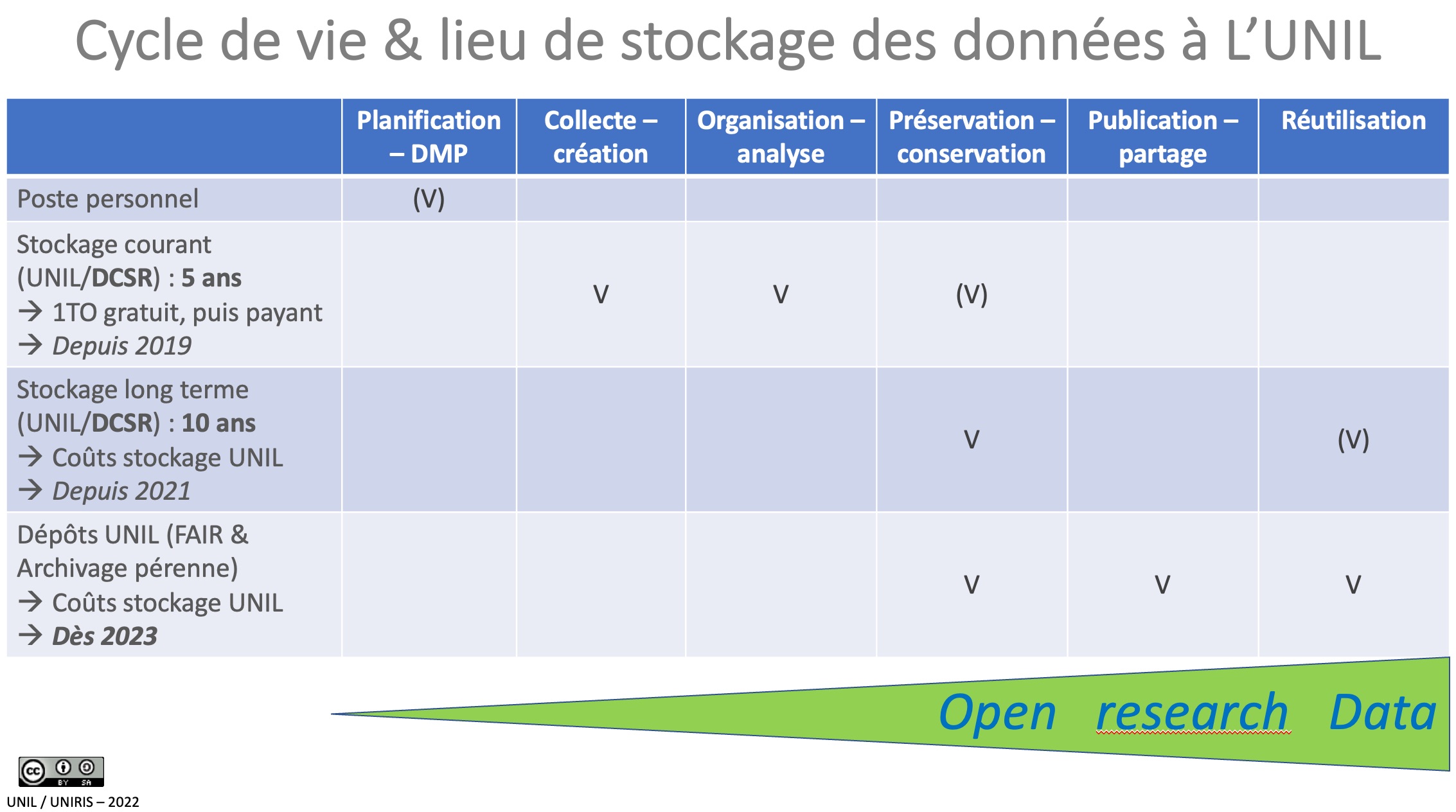
Current storage of research data
To meet the needs of its researchers for high-performance scientific computing, high-performance scientific computing advice and research data storage, the UNIL Directorate has created a Research Computing and Support Division (DCSR) whose infrastructures are managed and maintained by the UNIL Computer Centre.
The DCSR provides researchers with an organized and sized infrastructure to meet the variety of storage needs (sensitive or non-sensitive data) encountered in a high-performance computing environment.
In addition to the security aspect, hosting data at UNIL offers the following advantages :
- 1 or 2 copy(s) of the data.
- Possibility to recover the previous state of a file/folder for up to 3 months.
- Management of the volume of spaces by simple quota.
- Access in SMB/CIFS or NFS (v3).
Storage allows the use and backup of research data during the implementation phase of the Project. It is in principle limited to a maximum duration of 5 years from the end date of the Project. The UNIL secure storage service is invoiced, at cost price, by the Ci and is accompanied by management rules (creation of a Data Management Plan).
A current storage quota of 1TB is allocated free of charge by Ci. After this volume, storage costs will be charged.
The Rectorate's directive 4.5 defines the rules for using the secure storage spaces provided by UNIL.
Any researcher who wishes to benefit from storage space for his or her data must send his or her request to the DCSR : Request for Storage of Research Data.
The storage of research data on the cloud and in an unsecured way (no backup, no access control, no security on sensitive data, etc.) raises important legal and ethical questions. It is in principle prohibited by our Institution. For more information, contact UNIL's Division of Calculation and Research Support (DCSR).
For more information on storage and server services, see the dedicated pages of the IT Center.
Long-term storage of research data
Following the entry into force of the Rectorate Directive 4.5 Management and processing of research data, research data located on NAS storage space made available to faculties will have to be migrated to the institutional infrastructure dedicated to research (NAS Research Server).
The DCSR is currently working on the implementation of a long-term storage space (10 years) that can accommodate so-called "cold" data (completed projects). Unlike current storage space, which is not free of charge above 1TB, the costs associated with long-term storage are borne by UNIL. The data stored (transferred) must nevertheless be organized by project and accompanied by a readme file.
The model of this Readme will be automatically created at the root of your long-term storage space. Once your "cold" data has been transferred to this space, all you have to do is complete the Readme fields in order to describe and organize, at a minimum, your data.
Access the Readme and its accompanying guide.